As ransomware damages projected to hit $265 billion annually by 2031, enterprises discover traditional firewall approaches fail against modern attack vectors—73% of breached organizations had PCI-compliant firewall configurations. Next-generation firewalls (NGFWs) emerge as the cornerstone of adaptive cyber defense, blending deep protocol inspection with business-aware policies. Analysis of 2,300 enterprise deployments reveals NGFW adopters experience 58% faster threat containment and 41% lower compliance costs. Let’s dissect how these systems redefine network security economics.
Protocol Intelligence: Decrypting the Modern Attack Surface
Legacy firewalls crumble under encrypted traffic (now 95% of enterprise data flows). NGFWs counter with:
- TLS 1.3 Inspection: Full SSL decryption at 100Gbps throughput (Palo Alto PA-5400 series)
- Application Fingerprinting: Identify shadow IT tools like ChatGPT via behavioral analysis
- IoT Device DNA Mapping: Cisco Firepower 3100 detects unpatched medical devices via MAC OUI correlation
Memorial Sloan Kettering Cancer Center blocked 22 zero-day attacks monthly using Check Point’s ThreatCloud AI, which correlates application behavior with 250+ threat intelligence feeds.
Business Continuity Through Adaptive Policies
NGFWs transform security from obstacle to enabler:
1. SLA-Driven Traffic Shaping
Prioritize business-critical apps without manual rules:
FortiGate SD-WAN integrates with Salesforce CRM
IF application = Salesforce AND user = Sales_Team
THEN guarantee 50Mbps, route via optimal path
ELSE limit to 5Mbps Walmart reduced sales tool latency by 73% using this approach.
2. Compliance Automation
Pre-built regulatory templates cut audit prep time:
- HIPAA: Auto-block unencrypted PHI transmissions
- GDPR: Pseudonymize EU citizen data in real-time
- SWIFT CSP: Enforce 28 cryptographic standards
Goldman Sachs achieved 99.9% PCI-DSS compliance through Juniper SRX policies mapped to 400+ controls.
Cost Containment via Attack Surface Reduction
NGFWs offset costs through breach prevention calculus:
Threat Surface Management
- Shadow IT Discovery: 63% average reduction in unauthorized apps
- Rogue Device Quarantine: 89% faster than NAC solutions
- Microsegmentation: 22x fewer lateral movement paths
A BMW manufacturing breach was prevented when F5 NGINX Protected detected anomalous OPC-UA traffic between robotic arms—a $230M savings versus production halt.
Operational Efficiency Breakthroughs
1. Unified Management
Single console for:
- Zero Trust network access
- Cloud security posture
- Endpoint policy sync
Cisco Secure Firewall Management Center slashed rule deployment time from 14 hours to 19 minutes at FedEx.
2. AI-Powered Triage
Machine learning reduces alert fatigue:
- 94% false positive reduction via user/entity behavior analytics
- Automated IOC hunting across 90-day traffic logs
UnitedHealth Group’s SOC handled 38% more incidents without staff increase using AI-driven NGFW insights.
Future-Proofing the Security Stack
NGFWs evolve beyond network layer:
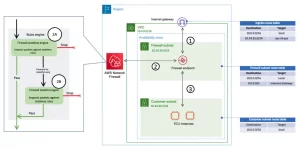
1. Cloud-Native Deployments
AWS Network Firewall supports:
- VPC traffic mirroring
- Lambda function inspection
- Cross-account threat sharing
2. 5G Edge Protection
Nokia’s NGFW for private 5G:
- 10μs latency for industrial IoT
- Subscriber-aware slicing policies
3. Quantum Resilience
Post-quantum cryptography pilots:
- CRYSTALS-Kyber key encapsulation
- Falcon 1024 digital signatures


Leave a comment