Ransomware isn’t just louder now; it’s smarter. Far beyond noisy smash-and-grabs, these attacks operate with chilling precision, quietly slipping past outdated defenses. That’s the reality for security teams battling the current wave. Recent analysis tracking major ransomware crews reveals an alarming shift: attackers now favour legitimate credentials swiped via phishing, often followed by hammering known – or even brand-new – weaknesses in systems exposed to the internet. Think critical apps, forgotten servers, anything facing the public. Gaining that initial foothold is just step one. Once inside, they morph into silent tenants, meticulously disabling your antivirus, hiding malicious code within legit-looking processes, and mapping every corner of your network. Their goal? To dig in deep, steal your crown jewels, and hit you twice – locking data andthreatening to leak it. This isn’t chaos; it’s targeted, calculated theft designed to exploit any sliver of weakness in your infrastructure. Old routers? Unpatched firewalls? They’re practically holding the door open. Understanding this evolution isn’t academic; it’s survival for your business’s core data and reputation. The tactics are clear; the defense needs to be sharper.
Attackers aren’t just breaking in; they’re logging in. Cisco Talos’ deep dive into nearly a dozen major ransomware gangs confirmed what frustrates defenders daily: stolen passwords opened the door in a huge number of cases. Forget Hollywood hackers brute-forcing firewalls; why bother when a convincing email trick grants easy access? And that initial phish is rarely the end of it. Exploiting known bugs in public-facing software is the favored next move – gaps that should’ve been patched months ago become superhighways for criminals. It’s a brutal combo: human error meets forgotten vulnerabilities.
This ransomware landscape keeps changing shape. Forget single megagroups; it’s all about specialization now. Players like Hunters International and Akira carve out niches, tailoring their attacks for specific industries or payout structures. These aren’t one-trick ponies either. Once nestled within your network, they vanish – switching off security tools like AV and endpoint protection. They pack their malicious tools tight, letting them unravel silently in your system’s memory, then tweak registries to kill warnings and ensure they start up every boot. Persistent pests, indeed.
Think MFA makes you safe? Think harder. Clever attackers sidestep it entirely by finding flaws or misconfigs in how your MFA is set up, especially on old or unpatched internet-facing systems. It’s a painful reality check. Their mission? Don’t just visit; stay. Using tricks like auto-starting malware on boot or setting up sneaky backdoors with remote access tools, they guarantee long-term residency. Then the real snooping begins. With persistent access secured, they meticulously explore. They chart your entire network layout, locate critical servers and sensitive data stores – essentially creating a treasure map for extortion. Common network scanning tools blend in perfectly with everyday admin tasks, turning your own utilities into delivery trucks for more malware. And the payout? Doubling down. They hunt for critical info – financials, customer records, R&D – packing it up discreetly using utilities everyone knows (WinRAR, 7-Zip) or custom exfil tools like LockBit’s StealBit. They don’t just hold your files hostage; they threaten to spill your secrets too. These groups act more like Advanced Persistent Threats (APTs), not just smash-and-grabbers. They’re patient, sneaky invaders aiming to linger unseen, plucking valuable data or setting the stage for an even bigger future assault. Aged infrastructure and flaky edge devices are their paradise, riddled with known, but tragically unpatched, holes.
Beating this evolving menace demands concrete, practical action. Let’s ditch the fluff:
1.
Patching Isn’t Optional; It’s Urgent: Ignoring updates is playing Russian roulette. Consistently applying patches for EVERYTHING – routers, switches, servers, apps, workstations – is the absolute bedrock defense. Those CVEs vendors scream about? They’re literal roadmaps for attackers. Patch. Promptly. Especiallyon anything exposed externally.
2.
Passwords Need Muscle & MFA: “Password123” just won’t cut it anymore. Mandate complex, unique passwords for every single accountand system. Period. Combine this with rock-solid Multi-Factor Authentication (MFA) enforcement. No excuses. SMS might be vulnerable, so use an authenticator app or security keys where feasible. It adds the crucial friction attackers hate.
3.
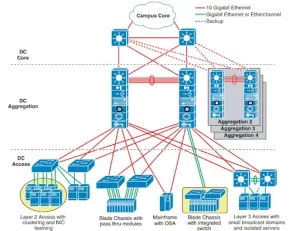
Segment Ruthlessly & Lock Doors: Running one giant flat network? You’re handing attackers the keys to the kingdom. Segmentation – isolating critical servers and sensitive data zones behind internal firewalls (like next-gen ASA firewalls) – is non-negotiable. If they breach a marketing PC, they shouldn’t glide straight into finance or HR databases. Pair this with strict network access control (like Cisco ISE implementing 802.1X) to ensure ONLY known, authorized devices can physically connect to your network ports. Keep the riff-raff out at the door.
4.
Watch Like a Hawk & Hunt Threats: Security through obscurity is dead. Invest in visibility. Security Information and Event Management (SIEM) systems like Cisco SecureX act as your 24/7 nerve center, correlating logs and spotting anomalies across your Cisco gear. But visibility alone isn’t defense. Deploy Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) solutions (like Cisco Secure Endpoint) aggressively. These tools hunt for malicious activity in progress, investigating threats and enabling response even on encrypted traffic – far beyond basic signature-based antivirus. Think proactive hunting, not just passive blocking.
Choosing reliable, high-performance networking equipment is more than an upgrade; it’s fundamental for building robust defenses. Outdated, unsupported routers and switches become security liabilities themselves – their vulnerabilities are prime targets, and their limited capability cripples segmentation and advanced threat detection. Implementing strong NAC requires manageable, enterprise-grade switches (like Catalyst 9000 series) across your access layer. Granular segmentation demands powerful firewalls (like Firepower Threat Defense) at critical boundaries. Effective EDR/XDR needs endpoints talking securely to central platforms – that requires a stable, modern network backbone. You can’t build a modern fortress on crumbling walls. For organizations serious about upgrading their network security posture with proven, powerful Cisco hardware – from core to edge – exploring your options through telecomate.com is a logical next step. They source genuine Cisco equipment, providing the building blocks you need to put these crucial recommendations into practice effectively.
Staying ahead of ransomware isn’t about silver bullets; it’s about relentlessly building resilience. Cisco Talos observations paint a stark picture: sophisticated attackers relentlessly exploit the weakest links – often legitimate credentials and overlooked patches on public-facing assets. The consequence isn’t just data loss; it’s operational paralysis, reputational collapse, and double extortion. The countermeasures outlined here – aggressive patching, ironclad passwords/MFA, strategic segmentation paired with strict NAC, and pervasive monitoring powered by EDR/XDR– form a robust defense-in-depth strategy. Critically, this strategy is impossible to implement effectively without a solid, modern network infrastructure. Outdated or underpowered switches, routers, and firewalls become the very bottlenecks attackers exploit, hindering segmentation efforts, crippling NAC deployment, and throttling the data flow essential for real-time threat hunting. Building serious cyber resilience means investing in both the strategy andthe robust, manageable hardware foundation it runs on. Upgrading your networking core isn’t just an IT project; it’s a fundamental security necessity. telecomate.com delivers the genuine Cisco routing and switching solutions required to transform those strategic recommendations into concrete, operational defenses capable of meeting the sophisticated ransomware threat head-on. Protect your business from the ground up.


Leave a comment