If you’ve ever managed a network switch, you know it’s not just about connecting devices—it’s about controlling how they communicate. One of the most effective tools for segmenting and securing network traffic is the use of VLANs, or Virtual Local Area Networks. Essentially, VLANs allow you to break a physical network into logical segments, each acting as an isolated broadcast domain. But not all VLANs are the same. Depending on the type of traffic they carry or the function they perform, VLANs can be categorized in ways that directly impact network design, security, and performance. From the default VLAN that every switch port initially joins, to specialized voice and management VLANs, understanding these variations helps you build more resilient, efficient, and secure networks. Whether you’re configuring a new switch or optimizing an existing infrastructure, knowing which VLAN type to use—and when—can significantly simplify traffic management and reduce vulnerabilities.
Default VLAN: The Starting Point
When you first boot up a switch, every port is automatically assigned to a default VLAN—usually VLAN 1 on Cisco devices. This makes all ports part of the same broadcast domain, allowing connected devices to communicate freely. However, there’s a catch: VLAN 1 can’t be renamed or deleted, and it’s also used for critical Layer 2 control protocols like CDP and STP. While convenient, using VLAN 1 as your default isn’t recommended from a security standpoint. Best practice is to reassign ports to a different, user-defined VLAN and reserve VLAN 1 only for control traffic. This limits exposure to unauthorized access and network attacks.
Data VLAN: Focusing on User Traffic
A data VLAN is dedicated solely to user-generated data. This means it doesn’t handle management or voice traffic—it’s all about the everyday data moving across your network. Isolating user traffic into a data VLAN improves both security and performance. You reduce unnecessary broadcast traffic and create clearer boundaries between different types of network services. It’s a foundational practice for anyone serious about building organized, scalable networks.
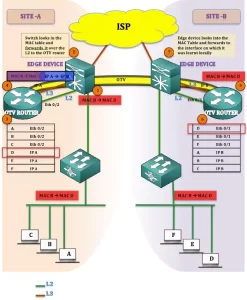
Native VLAN: Handling Untagged Traffic on Trunks
On an 802.1Q trunk port, the native VLAN serves a specific purpose: it carries traffic that isn’t tagged with a VLAN ID. This is essential for maintaining compatibility between devices and supporting legacy systems that may not support VLAN tagging. However, misconfiguration can lead to security risks. If the native VLAN is left as default (VLAN 1) on both ends of a trunk, it might expose control traffic. Always ensure the native VLAN is consistent across trunk links and different from your data or management VLANs.
Management VLAN: Secure Switch Access
The management VLAN is configured specifically for accessing your switch’s management interfaces, like SSH or web-based tools. You assign an IP address to this VLAN, allowing remote administration. It’s a good idea to use a VLAN other than VLAN 1 for management purposes. Isolating management traffic from user data helps prevent unauthorized access and adds a layer of security. If someone gains access to a user port, they still won’t easily reach your management plane.
Voice VLAN: Prioritizing Real-Time Communication
Voice VLANs are optimized for voice traffic, often associated with VoIP phones. They prioritize real-time communication to ensure high call quality and minimal delay. Typically, voice VLANs are configured to give precedence to voice packets over other data types—this is where QoS (Quality of Service) settings play a key role. Properly configuring a voice VLAN means assigning it to switch ports connected to IP phones, setting trust boundaries, and making sure bandwidth is reserved. This isn’t just convenient; it’s necessary for clear, uninterrupted voice communication across your network.
Each type of VLAN serves a distinct purpose, and using them correctly can dramatically improve the functionality and security of your network. Whether it’s keeping management traffic separate, prioritizing voice, or simply organizing user data, VLANs help you design a cleaner and more controlled network environment. For network administrators and engineers working with switches and routers, mastering VLANs is not optional—it’s essential. As networks grow in complexity, the ability to logically segment traffic using VLANs will continue to be a cornerstone of effective network design. For more detailed configuration guides and best practices, visit telecomate.com.


Leave a comment