Network administrators constantly grapple with balancing accessibility and security in dynamic environments. One critical tool for safeguarding infrastructure is MAC address filtering—a method to block unauthorized devices from accessing your network. For organizations relying on Huawei switches, mastering this feature isn’t just about technical compliance; it’s about building a proactive defense against breaches. But how effective is device-level control in an era of evolving cyber threats? Let’s dissect the process while addressing its broader implications for network integrity.
Why Blocking MAC Addresses Matters
Every device connected to a network has a unique MAC address, acting like a digital fingerprint. By restricting access to trusted devices, administrators reduce risks like unauthorized data leaks or rogue hardware infiltrations. Huawei switches simplify this process through intuitive configurations, but the real value lies in aligning these controls with broader security policies.
Step-by-Step: Blocking MAC Addresses on Huawei Switches
1. Access the Switch Interface
Connect to the Huawei switch via console cable or SSH. Use terminal software (e.g., PuTTY) and log in with administrator credentials. Navigate to system view with system-view.
2. Create an ACL Rule
Define an Access Control List (ACL) to target specific MAC addresses. For example:
acl name Block_MAC basic
rule 5 deny source-mac XXXX-XXXX-XXXX Replace XXXX-XXXX-XXXX with the unauthorized device’s MAC address.
3. Apply the ACL to an Interface
Bind the ACL to the relevant port or VLAN. For instance:
interface GigabitEthernet 0/0/1
traffic-filter inbound acl name Block_MAC This blocks traffic from the specified MAC address on port 0/0/1.
4. Verify and Save Configuration
Check rules with display acl name Block_MAC. Confirm enforcement by testing connectivity from the blocked device. Save settings with save to prevent loss after reboots.
Beyond Basics: Optimizing MAC Filtering
While blocking individual addresses works for small networks, scaling requires smarter strategies. Combine MAC filtering with:
- Port Security: Limit the number of devices per port.
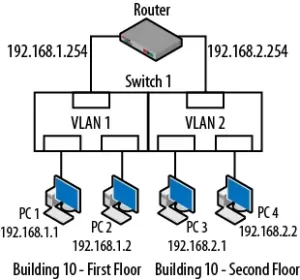
- Dynamic VLANs: Automate access based on device roles.
- Monitoring Tools: Use Huawei’s eSight software to track anomalies in real time.
These layers ensure that even if a malicious device spoofs a trusted MAC address, additional safeguards mitigate risks.
Is Device-Level Control Enough for Modern Networks?
Blocking MAC addresses on Huawei switches is a foundational step, but it’s not a silver bullet. Modern threats like MAC spoofing or IoT vulnerabilities demand a hybrid approach. For example, pairing MAC filtering with 802.1X authentication adds identity verification, while regular audits prune obsolete rules.
Organizations must also train teams to update ACLs as devices rotate. A static rule blocking a contractor’s laptop yesterday could hinder a legitimate employee tomorrow. Balance rigidity and flexibility by integrating MAC controls into a centralized security framework.
In an age where network breaches cost millions, granular controls like MAC address blocking on Huawei switches remain indispensable. They empower administrators to enforce boundaries without crippling operational agility. However, their true potency emerges when fused with adaptive policies and continuous oversight. Whether securing a campus network or a data center, the goal isn’t just to block—it’s to build resilience through precision. After all, in cybersecurity, the smallest oversight can become the widest breach.








Leave a comment